Run automatic assessments of how the usage, employee access, cyber posture, and data sensitivity of your systems impact your organization.
Click here to get started with your Data Inventory.
To get started with Business Impact Assessments, be sure to add data sources to your Data Inventory. You can access Business Impact Assessments on the lefthand toolbar of your portal, under the "Compliance" tab.
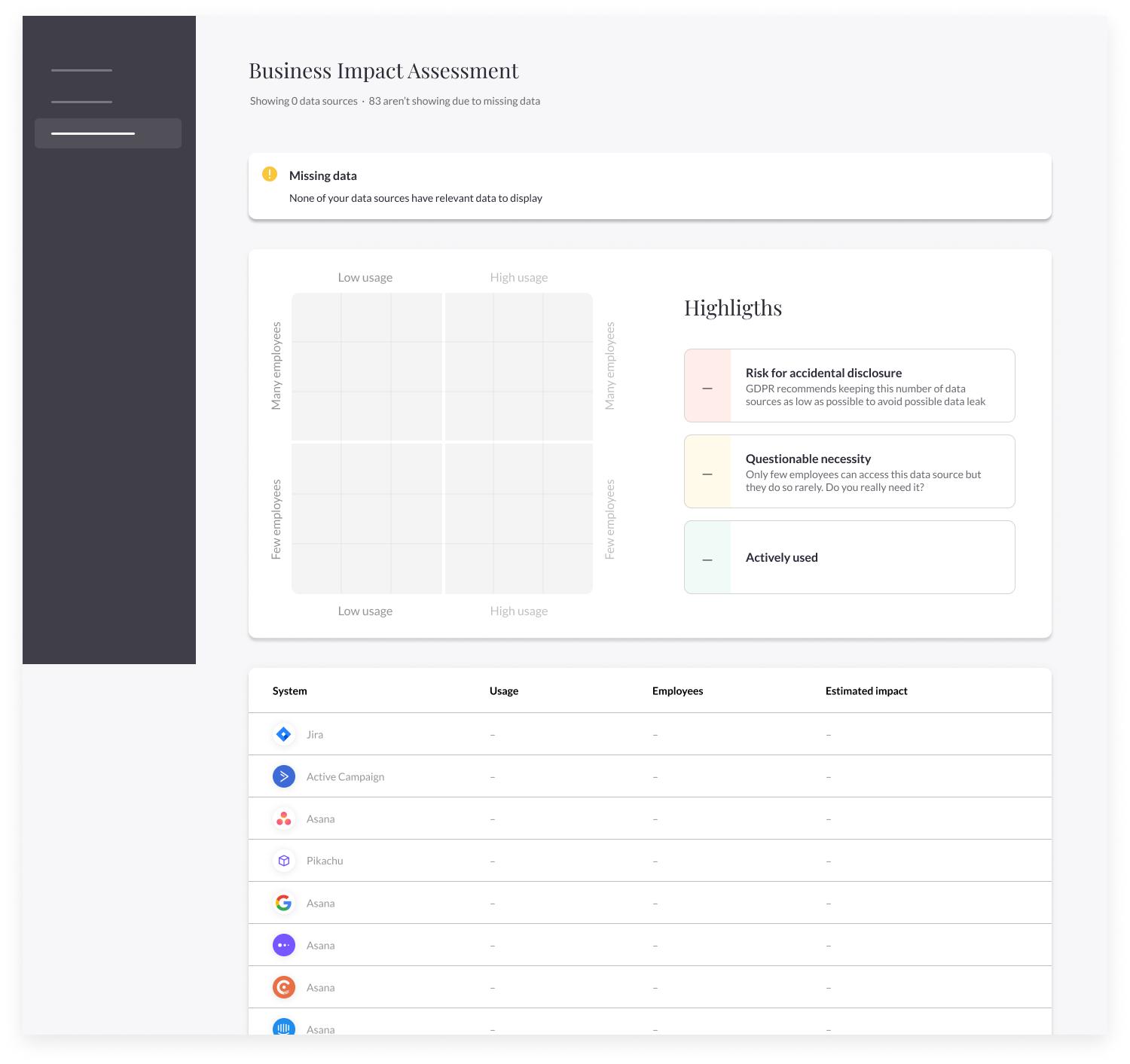
Business Impact Assessments will not be available until the relevant details for each data source is completed. To add this information, click on each data source and complete the fields in the source's "General" component.
-png.png)
After completing a system's usage details, remember that you can send the information for review to a data owner or relevant colleague.
After adding usage data to company systems, the "Estimated impact" column will display a data-driven risk analysis of each system to identify critical business functions and define associated risks.
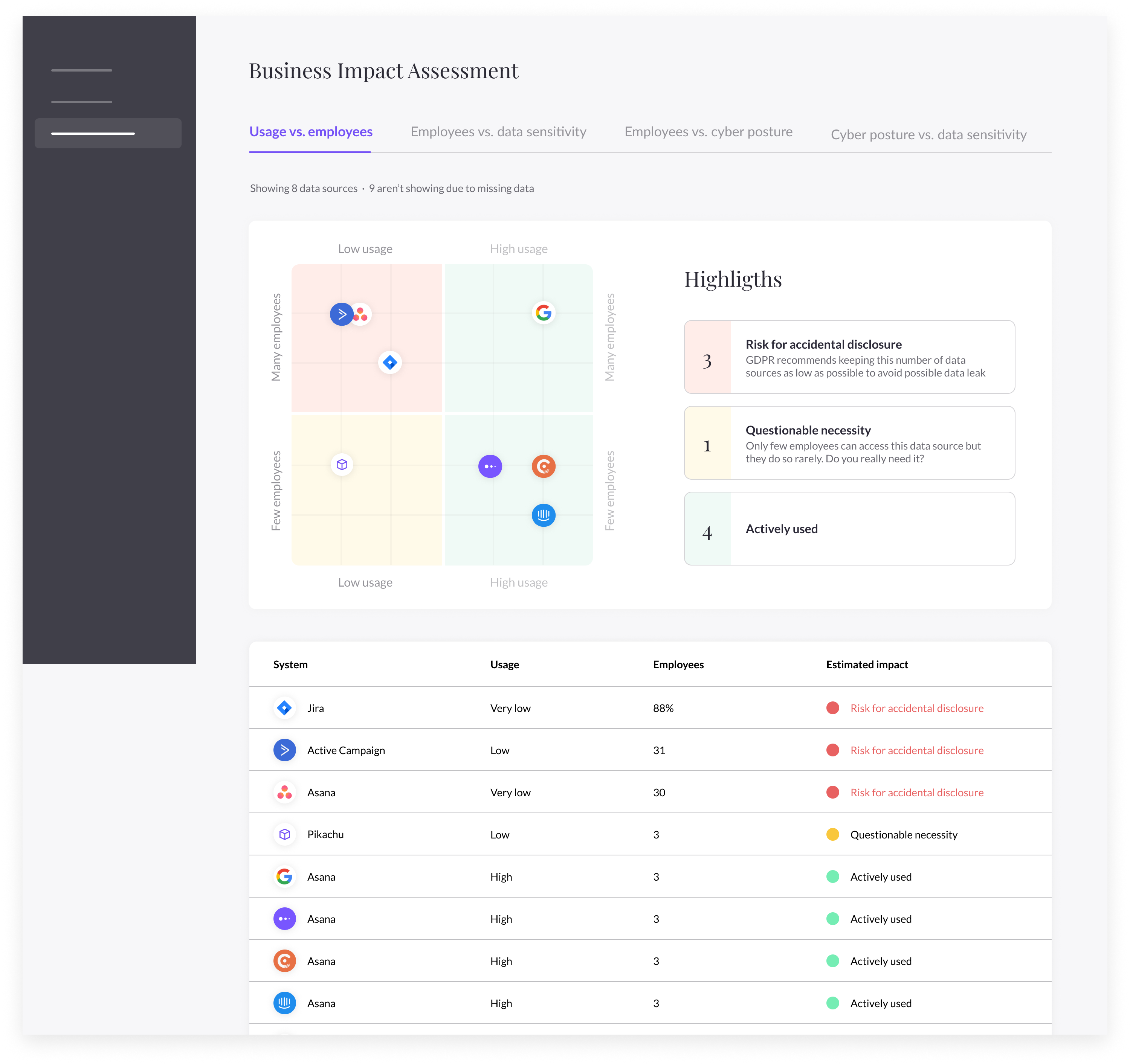
There are four business impact assessments:
- Usage vs. employees
- Employees vs. data sensitivity
- Employees vs. cyber posture
- Cyber posture vs. data sensitivity
The business impact assessments will help to determine systems that are not critical to business operations, discover nonessential employee access, and suggest improved security for higher-risk systems.
If you have questions about Business Impact Assessments, talk to us at portal@saymine.com, and we'll be happy to help! 🙂
Next steps:
- Learn about automated vendor risk assessments in MineOS
